Cyber Security Staffing Models
Executive Summary
Outsourcing corporate functions and business processes is as common in modern business lexicon as computers. Although outsourcing may seem like a recent phenomenon, it has a longstanding history originating from the early days of the United States. During the early years of America, the manufacturing of clippers ships sails was sent to Scotland, and the raw material came from India (Ghimire, 2005). So, what about outsourcing a modern day corporate cyber security department?
This section will compare and contrast three options for staffing a cyber security department; complete in-house staffing model, a hybrid model where most is outsourced while some remains in-house and finally, a fully outsourced model. Further, the paper will provide security considerations across all three and a framework to assist decision makers into selecting the right model for their enterprise.
Outsourcing corporate functions and business processes is as common in modern business lexicon as computers. Although outsourcing may seem like a recent phenomenon, it has a longstanding history originating from the early days of the United States. During the early years of America, the manufacturing of clippers ships sails was sent to Scotland, and the raw material came from India (Ghimire, 2005). So, what about outsourcing a modern day corporate cyber security department?
This section will compare and contrast three options for staffing a cyber security department; complete in-house staffing model, a hybrid model where most is outsourced while some remains in-house and finally, a fully outsourced model. Further, the paper will provide security considerations across all three and a framework to assist decision makers into selecting the right model for their enterprise.
Organizational Structure of the Cyber Security Function
Organizational strategy is the basis for the long-term direction of the enterprise; the strategy guides efforts, roles and responsibilities throughout the rest of the organization (McCready, n.d.). Therefore, determining where the security function reports within the organization needs to be determined prior to establishing the right staffing model. However, there are inherent biases that come with every reporting line option for the CISO and it is important to not allow these biases to corrupt the mission of the CISO. Best practices suggest the CISO report to the CIO (Touhill & Touhill, 2014). However, the goals for the CISO could be at times in direct conflict with the agenda for the CIO. For example, the CIO might inadvertently exercise undue influence on the CISO that would compromise security measures to meet an ERP deployment schedule. If the CISO reports to the CFO poses yet another conflict or bias in favor of risk or cost avoidance. Current research suggests the CISO reporting line is trending towards the top levels of the organization; 40% report to the CEO, 27% directly to the board of directors and only 24% are now reporting to the CIO (Fruhlinger, 2018). What organizational structure is optimal? There is no universal best practice for all companies in every industry. Further, measuring optimality is likely different across industry segments. However, Figure 1 below provides the results of one survey that measures the alignment strategy in terms of financial loss from security incidents as a function of where the CISO reports.
Organizational strategy is the basis for the long-term direction of the enterprise; the strategy guides efforts, roles and responsibilities throughout the rest of the organization (McCready, n.d.). Therefore, determining where the security function reports within the organization needs to be determined prior to establishing the right staffing model. However, there are inherent biases that come with every reporting line option for the CISO and it is important to not allow these biases to corrupt the mission of the CISO. Best practices suggest the CISO report to the CIO (Touhill & Touhill, 2014). However, the goals for the CISO could be at times in direct conflict with the agenda for the CIO. For example, the CIO might inadvertently exercise undue influence on the CISO that would compromise security measures to meet an ERP deployment schedule. If the CISO reports to the CFO poses yet another conflict or bias in favor of risk or cost avoidance. Current research suggests the CISO reporting line is trending towards the top levels of the organization; 40% report to the CEO, 27% directly to the board of directors and only 24% are now reporting to the CIO (Fruhlinger, 2018). What organizational structure is optimal? There is no universal best practice for all companies in every industry. Further, measuring optimality is likely different across industry segments. However, Figure 1 below provides the results of one survey that measures the alignment strategy in terms of financial loss from security incidents as a function of where the CISO reports.
Figure 1 – Financial Loss as a Function of the CISO Reporting Line (Fruhlinger, 2018)
|
Having the CISO report directly to the CEO or even to the BoD not only appears to show a lower financial loss from cyber incidents but also provides direct and immediate flow of information. This allows the CEO to keep the board informed and engaged and ensures security remains a priority and an integral part of the company’s strategy.
|
Training and Maintaining an In-House IT Staff
There are several advantages to an in-house model for the cyber security staff. First, it can minimize the risk to sensitive data and compliance issues to companies’ subject to regulatory compliance requirements as the accountability remains within the four walls of the organization. Second, having the cyber security team co-located with the business stakeholders allows them to collaborate more efficiently on business initiatives and the security controls that are required to support them.
The risk to a complete in-house model is staffing and retention. For example, monitoring is a cyber security function that never sleeps, this is a 24X7, 365 days per year task characterized by long periods of boredom followed by short bursts of panic, followed by more boredom (Schneier, 2003). The attacks are so infrequent on a single enterprise that it is difficult to keep these highly skilled staff members interested, thus enticing them to leave. This also represents a higher training burden for the enterprise as the range of threats they experience is so narrow, they will require additional training to be prepared for unfamiliar attacks. Further, the shortage in cybersecurity talent continues to get worse. It is expected the global cyber security workforce will have 1.5 million unfilled positions by the year 2020 (Zadelhoff, 2017). For a single enterprise, staffing and retention will become a hurdle as they need to compete more aggressively to attract, retain, and train the necessary talent.
There are several advantages to an in-house model for the cyber security staff. First, it can minimize the risk to sensitive data and compliance issues to companies’ subject to regulatory compliance requirements as the accountability remains within the four walls of the organization. Second, having the cyber security team co-located with the business stakeholders allows them to collaborate more efficiently on business initiatives and the security controls that are required to support them.
The risk to a complete in-house model is staffing and retention. For example, monitoring is a cyber security function that never sleeps, this is a 24X7, 365 days per year task characterized by long periods of boredom followed by short bursts of panic, followed by more boredom (Schneier, 2003). The attacks are so infrequent on a single enterprise that it is difficult to keep these highly skilled staff members interested, thus enticing them to leave. This also represents a higher training burden for the enterprise as the range of threats they experience is so narrow, they will require additional training to be prepared for unfamiliar attacks. Further, the shortage in cybersecurity talent continues to get worse. It is expected the global cyber security workforce will have 1.5 million unfilled positions by the year 2020 (Zadelhoff, 2017). For a single enterprise, staffing and retention will become a hurdle as they need to compete more aggressively to attract, retain, and train the necessary talent.
A Hybrid Model – Most IT is Outsourced, Few Remain In-House
There are many reasons to consider outsourcing. The predominant sentiment is cost reduction. However, other factors like dissatisfied executives are with the service they receive form corporate service functions like IT, Human Resources and Finance. A recent McKenzie report found that only 30% of senior executives are satisfied with the service they receive from their corporate functions (Edlich, et al., 2017). NIST Special Publication 800-35 identifies six categories that drive the decision to outsource security staff, these represent a change in; strategic/mission, budgetary conditions, technical and architecture, organizational, personnel and policy/processes (Grance, et al., 2003).
There are four primary advantages to outsourcing a portion of the functions within the cyber security department to a 3rd party; aggregation of expertise, economies of scale, broader view of the internet and the attack are seen more frequently (Schneier, 2003). For the organization, this provides a cost-effective means of gaining access to specialized security tools and expertise on a shared basis (Chapple, 2013).
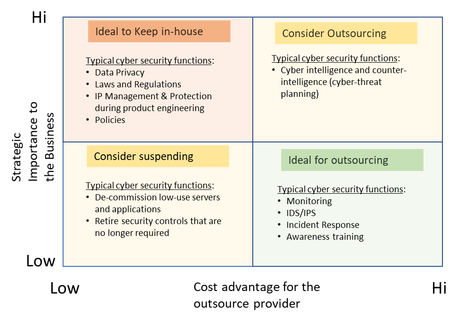
When considering a hybrid model, the CISO needs to make a risk-based decision on the specific cyber security functions to retain in-house. To do this, figure 2 below provides a framework to assist in the process. The X-axis represents the cost advantage for the outsource provider, the Y-Axis represents the level of strategic importance (high business context) to the business. Functions that are highly strategic to the business and have a low cost advantage for the outsource provider, are best to keep in-house; examples include, data privacy, IP protection during the engineering phase of new products and regulation compliance. Conversely, functions that are of low strategic importance and a high cost advantage for a 3rd party are candidates for outsourcing. These include; security monitoring, incident response and security awareness training.
The other two quadrants on the graph “consider outsourcing” and “consider suspending” are not as clear-cut for a decision to keep in-house or outsource, but are best suited for mid and long-term strategic discussions.
There are many reasons to consider outsourcing. The predominant sentiment is cost reduction. However, other factors like dissatisfied executives are with the service they receive form corporate service functions like IT, Human Resources and Finance. A recent McKenzie report found that only 30% of senior executives are satisfied with the service they receive from their corporate functions (Edlich, et al., 2017). NIST Special Publication 800-35 identifies six categories that drive the decision to outsource security staff, these represent a change in; strategic/mission, budgetary conditions, technical and architecture, organizational, personnel and policy/processes (Grance, et al., 2003).
There are four primary advantages to outsourcing a portion of the functions within the cyber security department to a 3rd party; aggregation of expertise, economies of scale, broader view of the internet and the attack are seen more frequently (Schneier, 2003). For the organization, this provides a cost-effective means of gaining access to specialized security tools and expertise on a shared basis (Chapple, 2013).
When considering a hybrid model, the CISO needs to make a risk-based decision on the specific cyber security functions to retain in-house. To do this, figure 2 below provides a framework to assist in the process. The X-axis represents the cost advantage for the outsource provider, the Y-Axis represents the level of strategic importance (high business context) to the business. Functions that are highly strategic to the business and have a low cost advantage for the outsource provider, are best to keep in-house; examples include, data privacy, IP protection during the engineering phase of new products and regulation compliance. Conversely, functions that are of low strategic importance and a high cost advantage for a 3rd party are candidates for outsourcing. These include; security monitoring, incident response and security awareness training.
The other two quadrants on the graph “consider outsourcing” and “consider suspending” are not as clear-cut for a decision to keep in-house or outsource, but are best suited for mid and long-term strategic discussions.
Figure 2 - Criteria for Outsourcing
IT Functions Fully Outsourced
Fully outsourcing the cyber security staff has the primary advantage of cost and gaining access to resources and capacity that would not normally be available, particularly for smaller organizations. Another advantage is the ability to scale, further validating the case for smaller companies in high-growth markets like tech firms. The primary risks remain as with the hybrid model but places greater emphasis on vendor selection, contracts (SLA’s) and governance. Many of these risks can be addressed with; greater due diligence over the provider’s security posture, ensuring contracts include information security, business continuity, privacy contracts and acceptance testing. Companies who utilize a full outsource model are encouraged to stipulate a right to audit within their contracts.
Fully outsourcing the cyber security staff has the primary advantage of cost and gaining access to resources and capacity that would not normally be available, particularly for smaller organizations. Another advantage is the ability to scale, further validating the case for smaller companies in high-growth markets like tech firms. The primary risks remain as with the hybrid model but places greater emphasis on vendor selection, contracts (SLA’s) and governance. Many of these risks can be addressed with; greater due diligence over the provider’s security posture, ensuring contracts include information security, business continuity, privacy contracts and acceptance testing. Companies who utilize a full outsource model are encouraged to stipulate a right to audit within their contracts.
Conclusion
Three outsourcing models for the cyber security department of an enterprise were discussed in this paper; full in-house, hybrid model and finally fully outsourced. An in-house staffing model has the advantage of control and close alignment with the business. Whereas both outsourcing models have the advantage of leveraging the broader pool of resources that provides additional expertise, capacity and scale that is not available in an in-house model. However, the risks are vastly different. The in-house model has the risk of employee turn-over with higher training costs whereas the outsourcing model is at “arm’s-length”, creating more risk to data privacy and questions of company viability. This approach shifts the burden to procurement teams to ensure contracts are tightly aligned with expected service levels. Regardless of the model, the responsibility to confidentiality, integrity and availability remains with the CISO and overall security remains with the executive team.
Three outsourcing models for the cyber security department of an enterprise were discussed in this paper; full in-house, hybrid model and finally fully outsourced. An in-house staffing model has the advantage of control and close alignment with the business. Whereas both outsourcing models have the advantage of leveraging the broader pool of resources that provides additional expertise, capacity and scale that is not available in an in-house model. However, the risks are vastly different. The in-house model has the risk of employee turn-over with higher training costs whereas the outsourcing model is at “arm’s-length”, creating more risk to data privacy and questions of company viability. This approach shifts the burden to procurement teams to ensure contracts are tightly aligned with expected service levels. Regardless of the model, the responsibility to confidentiality, integrity and availability remains with the CISO and overall security remains with the executive team.